Steampunk Spotter
Build Trust in Every Ansible Playbook
Ansible Playbook Platform that scans, analyzes, enhances, and provides insights for your playbooks.
TRUSTED BY





Speed up Ansible Upgrades
Quickly check Ansible version compatibility, resolve issues, and upgrade playbooks with ease.
Playbook Upgrade ScanningEnhance Playbook Security and Compliance
Identify potential vulnerabilities in your playbooks before they can be exploited, and ensure your automation adheres to relevant security standards.
Playbook Security ScanningNEW FEATURE
SBOM, CVEs and Security ReportsBring order to your playbooks
Create consistent, clear, and easily accessible Playbooks that ensure every team follows best practices in Ansible automation.
Playbook Best Practice ChecksUpgrade Ansible Playbooks
Speed up Ansible Upgrades
Quickly check Ansible version compatibility, resolve issues, and upgrade playbooks with ease.
Playbook Upgrade ScanningPlaybook Security and Compliance
Enhance Playbook Security and Compliance
Identify potential vulnerabilities in your playbooks before they can be exploited, and ensure your automation adheres to relevant security standards.
Playbooks Standardization
Bring order to your playbooks
Create consistent, clear, and easily accessible Playbooks that ensure every team follows best practices in Ansible automation.
Playbook Best Practice ChecksEnterprise features
Unlock the full power of your Ansible Playbook management with Spotter On-Prem — built for enterprises that need control, security, and advanced features.
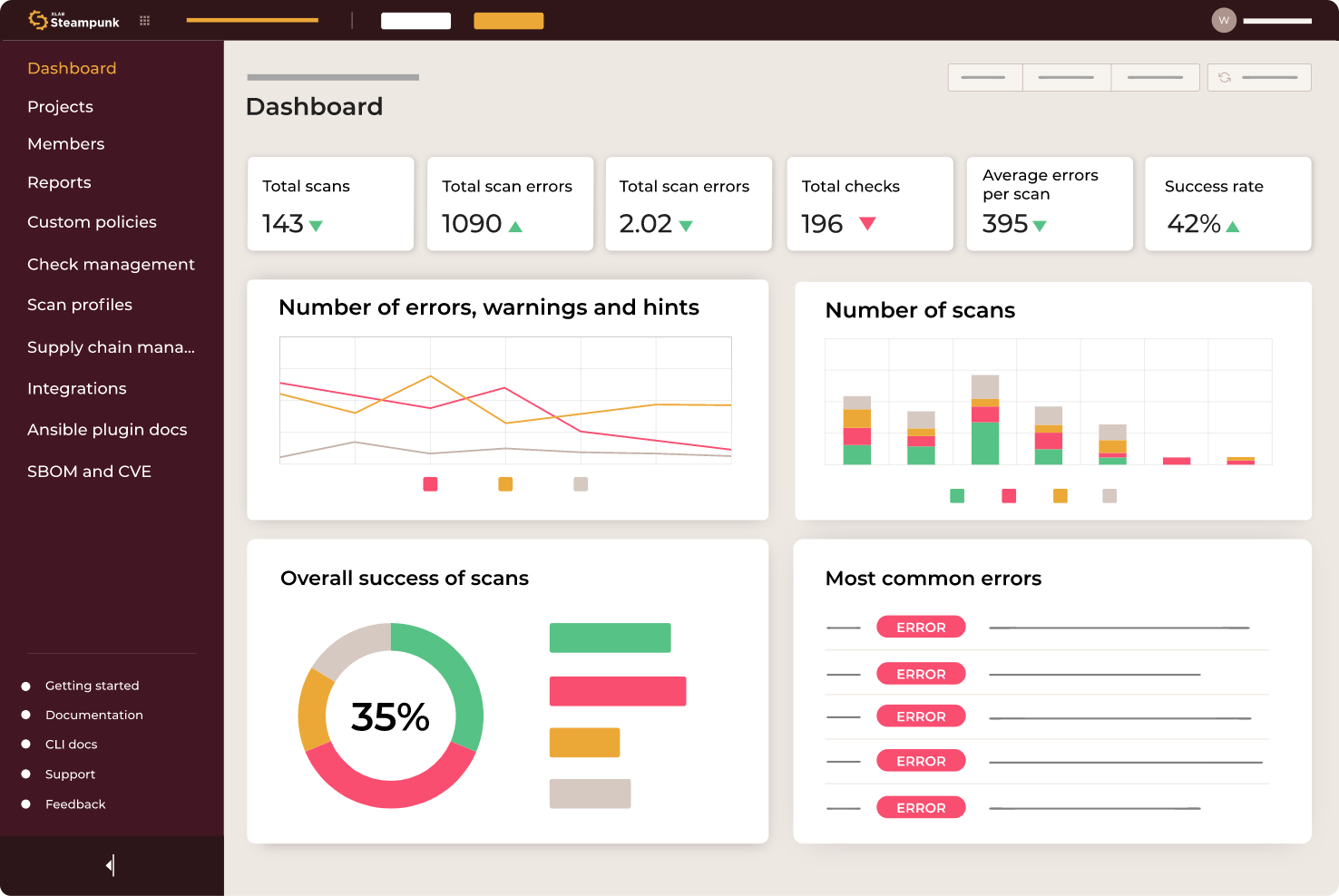
PERFORMANCE INSIGHTS
Analytics and reporting
Analyze scan data, spot trends, monitor progress, and create custom reports with the intuitive reporting feature. Focus on delivering results and make data-driven decisions.
INTEGRATIONS
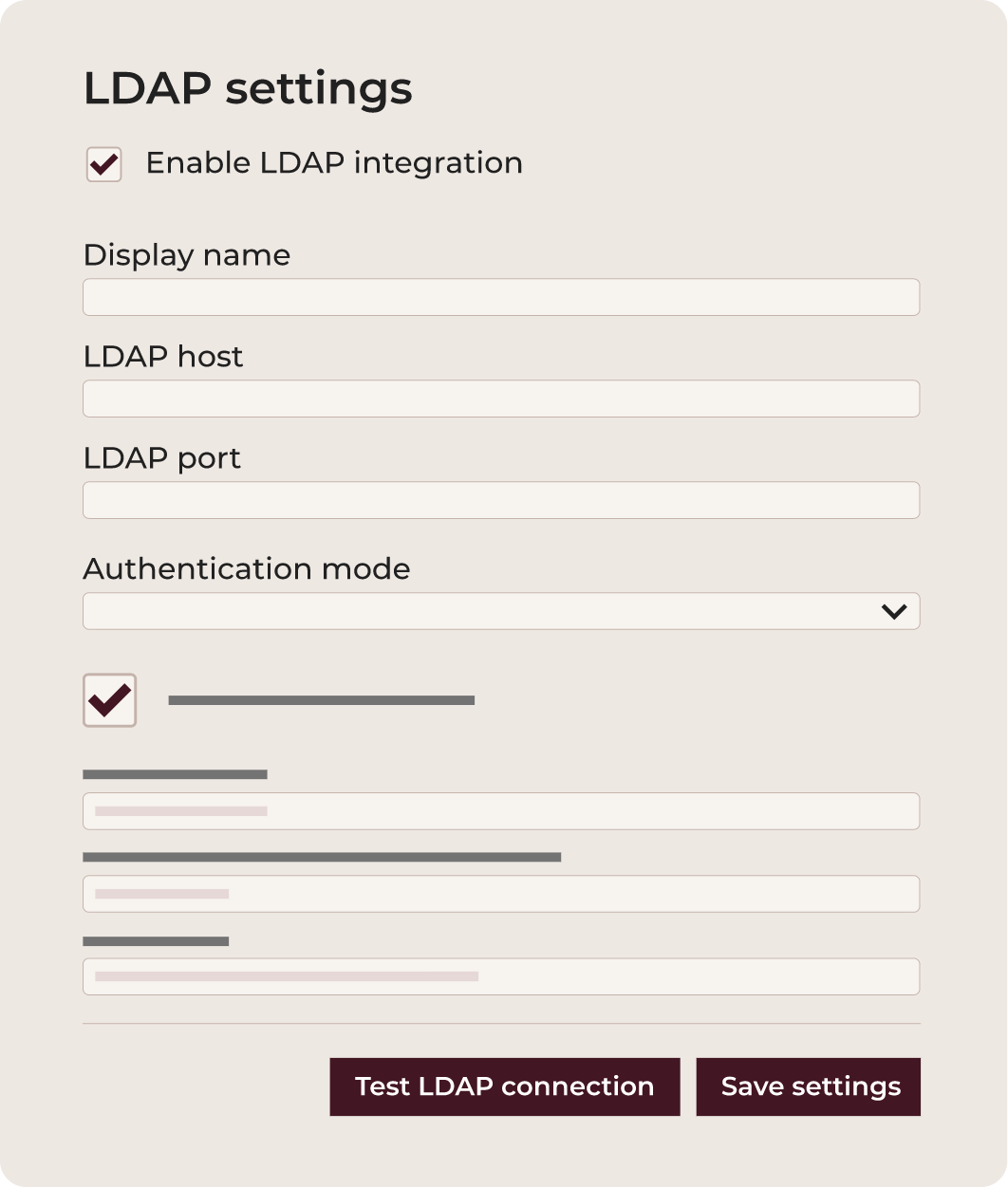
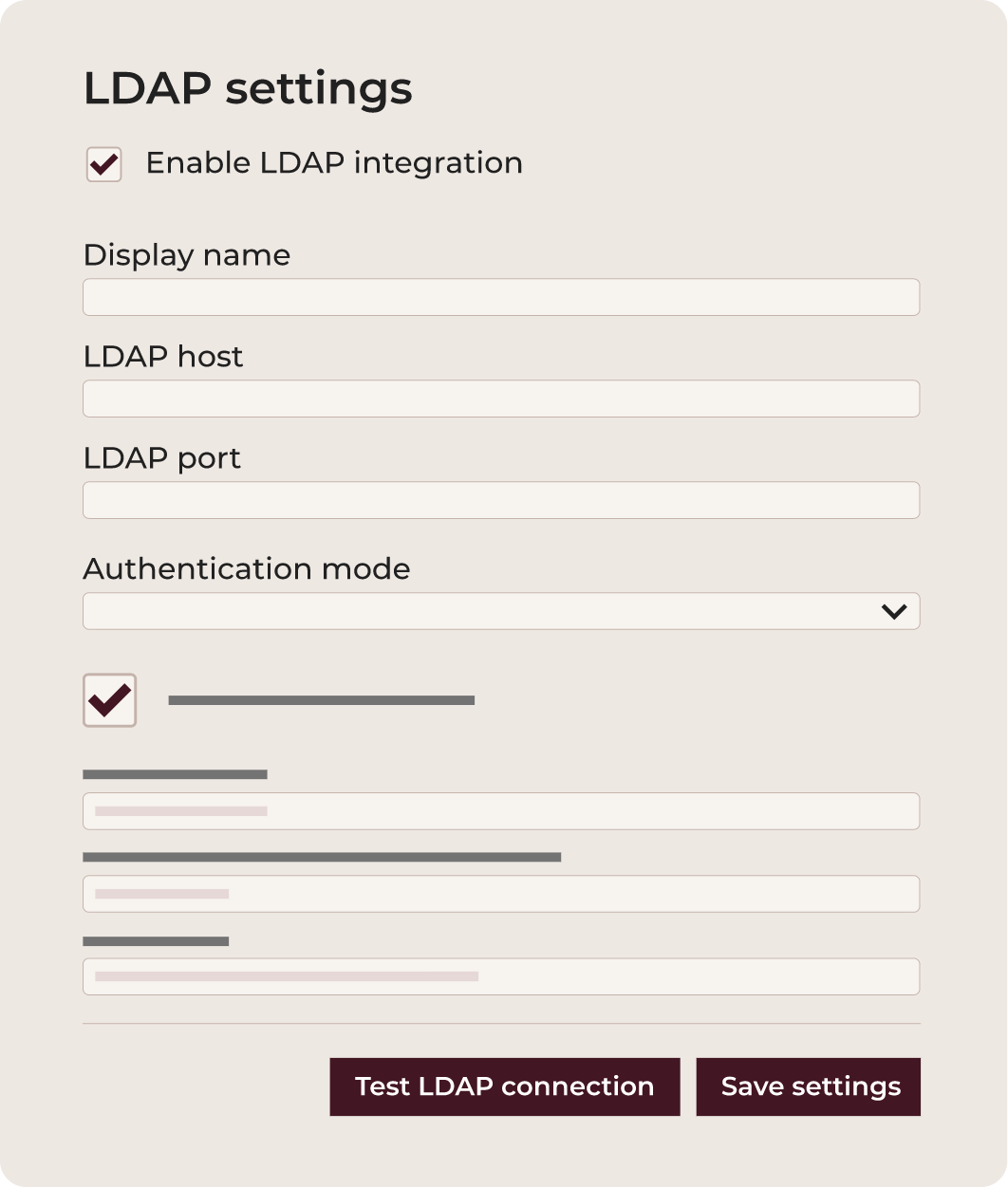
LDAP integration
Customize LDAP integration for on-premises installations, enable seamless user, group, and permission mapping without tiered limitations.
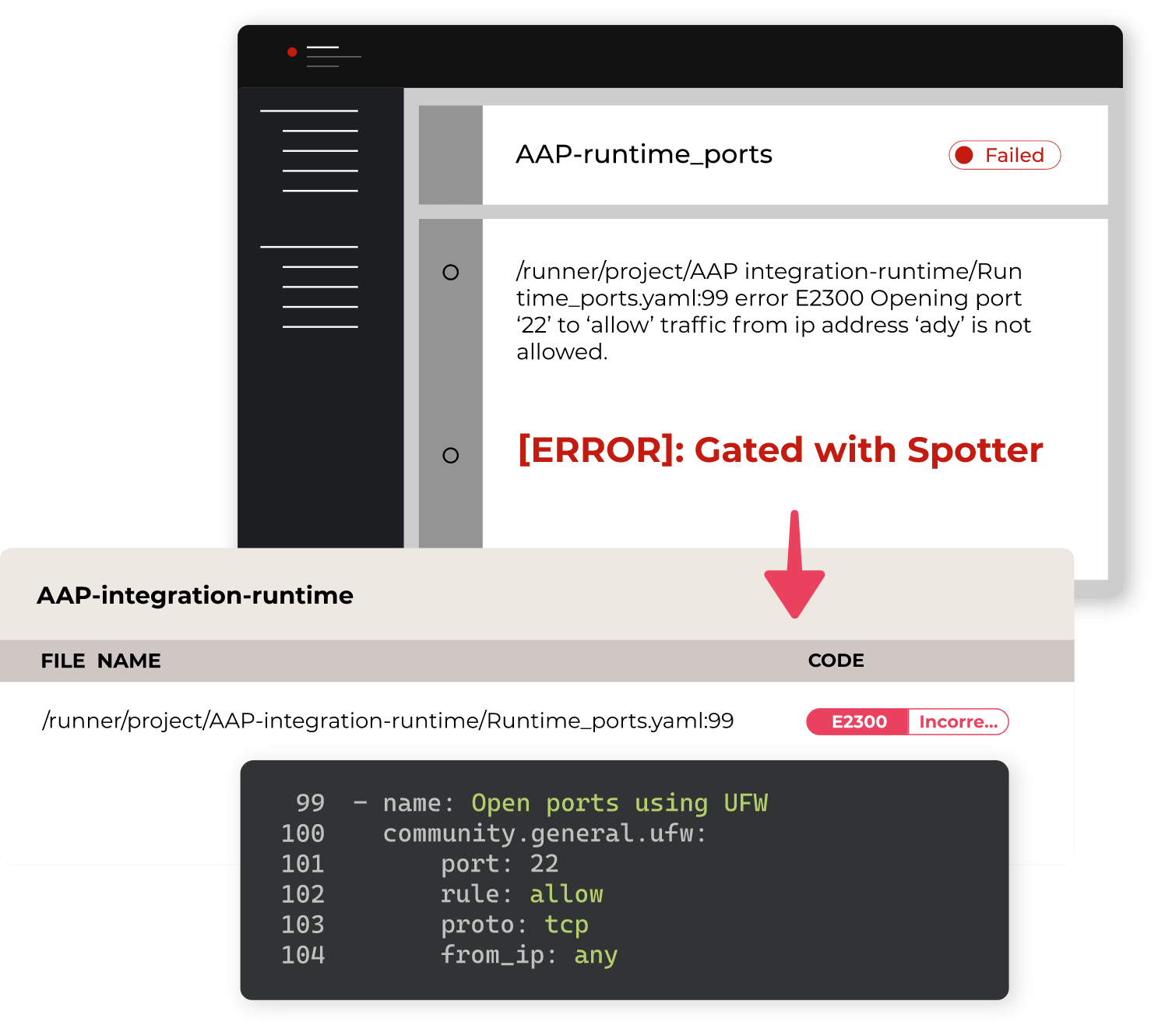
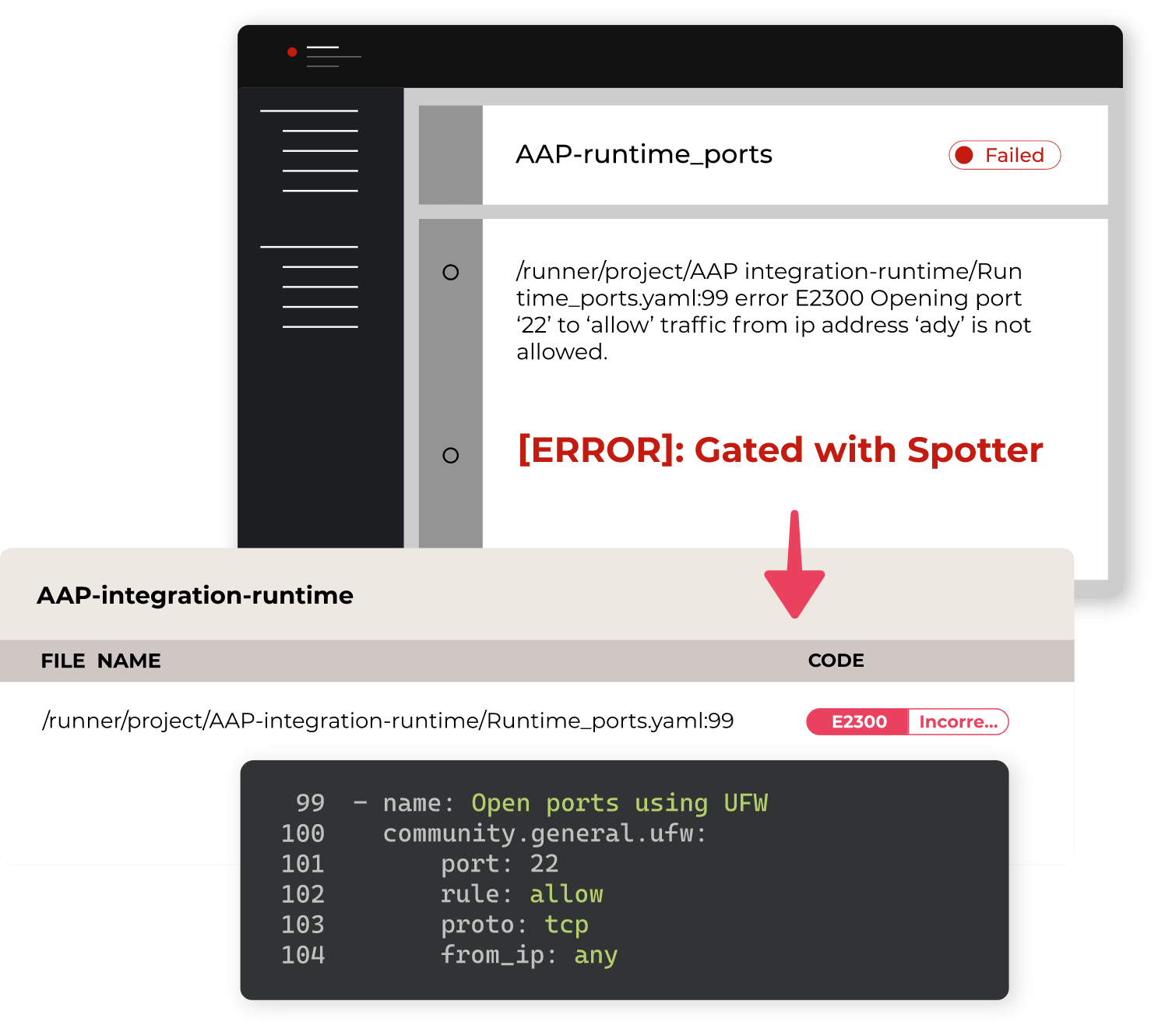
INTEGRATIONS
Integrate with Red Hat AAP
Check your Ansible content before and during execution in AAP. Prevent errors and ensure secure, compliant automation. This saves time by catching issues early.
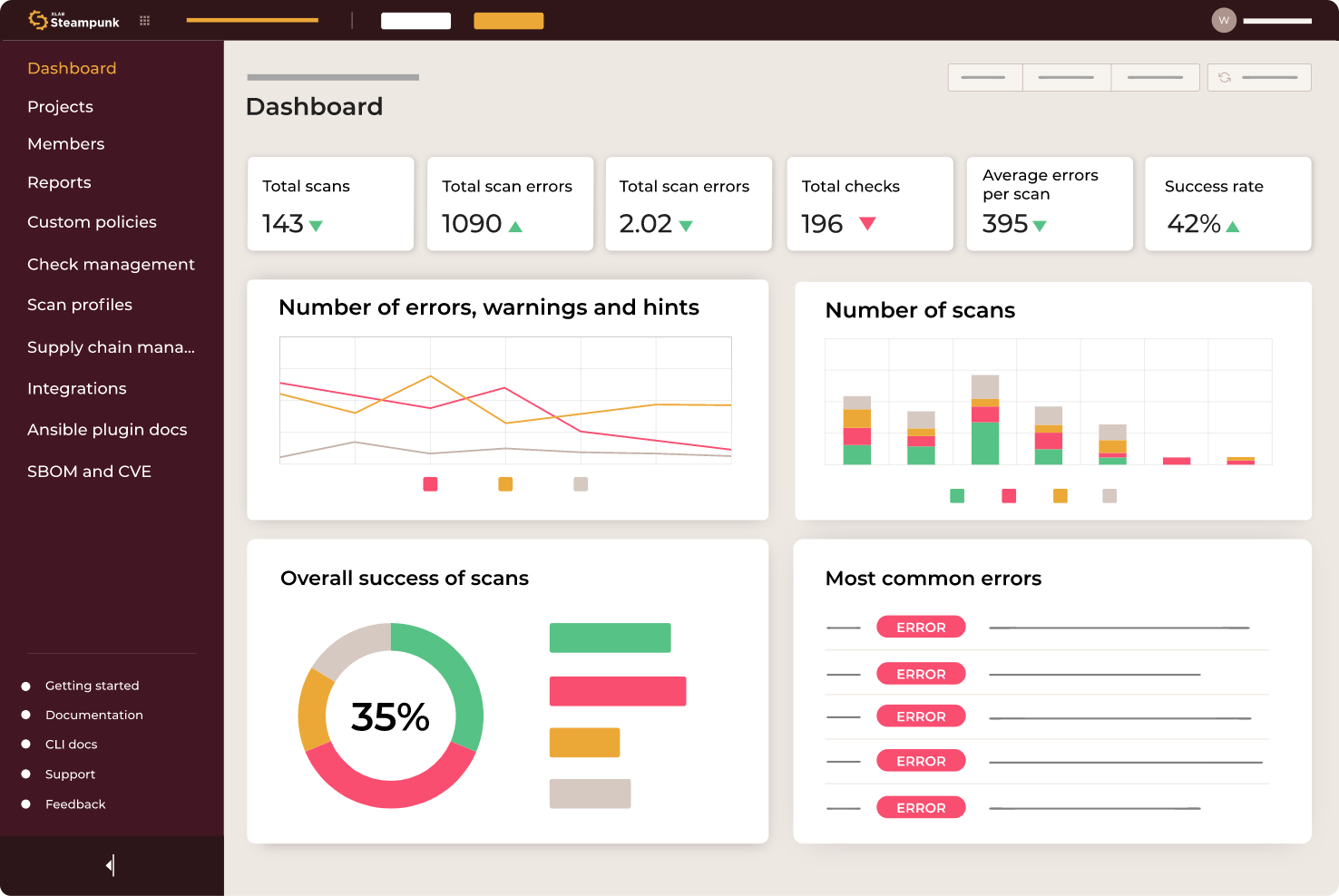
PERFORMANCE INSIGHTS
Analyze scan data, spot trends, monitor progress, and create custom reports with the intuitive reporting feature. Focus on delivering results and make data-driven decisions.
INTEGRATIONS
Customize LDAP integration for on-premises installations, enable seamless user, group, and permission mapping without tiered limitations.
INTEGRATIONS
Check your Ansible content before and during execution in AAP. Prevent errors and ensure secure, compliant automation. This saves time by catching issues early.
Fortune 100 FSI Saved 17000 hours using Steampunk Spotter
8x
faster migration
9 years
of work saved
82%
playbook errors reduction
413%
ROI

Sign up for free playbook assessment
Apply for a free, expert-led review of your own Playbooks with Steampunk Spotter and discover immediate insights, risks, and opportunities.
- Scan your playbooks for errors
- Evaluate the health of your playbooks
- Get a free expert consultation
- Receive a report of cost and time savings
Apply for assessment